Últimamente le están dando mucha caña a los CMS, wordpress y drupal suelen ser los que se están llevando todos los golpes. El otro día estuvieron escaneando vulnerabilidades sobre un site que no es wordpress. Aun así Modsecurity los paro antes. No había visto este tipo de mensajes nunca (en mis maquinas).
[Tue Sep 22 05:37:37.436341 2015] [:error] [pid 3969] [client 23.94.29.35] ModSecurity: Multipart parsing error (init): Multipart: Invalid boundary in C-T (characters). [hostname «xxxx.xx»] [uri «/wp-content/themes/ProjectTheme/lib/upload_main/upload.php»] [unique_id «VgDNAVt5CX8AAA@BCCEAAAAk»] [Tue Sep 22 05:37:37.537782 2015] [:error] [pid 3969] [client 23.94.29.35] ModSecurity: Access denied with code 400 (phase 2). Match of «eq 0» against «REQBODY_ERROR» required. [file «/etc/modsecurity/modsecurity.conf»] [line «63»] [id «200002»] [msg «Failed to parse request body.»] [data «Multipart: Invalid boundary in C-T (characters).»] [severity «CRITICAL»] [hostname «xxxx.xx»] [uri «/wp-content/themes/ProjectTheme/lib/upload_main/upload.php»] [unique_id «VgDNAVt5CX8AAA@BCCEAAAAk»] [Tue Sep 22 05:37:38.283834 2015] [:error] [pid 8957] [client 23.94.29.35] ModSecurity: Access denied with code 400 (phase 2). Match of «eq 0» against «REQBODY_ERROR» required. [file «/etc/modsecurity/modsecurity.conf»] [line «63»] [id «200002»] [msg «Failed to parse request body.»] [data «Multipart: Invalid boundary in C-T (characters).»] [severity «CRITICAL»] [hostname «xxxx.xx»] [uri «/uploadify/uploadify.php»] [unique_id «VgDNAlt5CX8AACL9EoMAAAAA»]
Y así durante algunas horas…
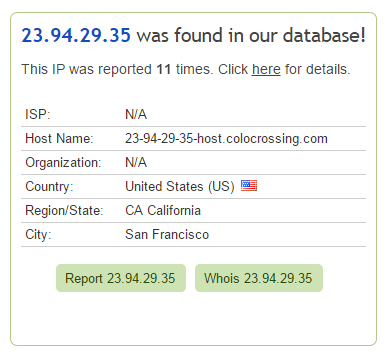
En cuanto se aburrió (o terminaron los test) se fue a otro sitio …